We’re excited to announce Go’s new assist for vulnerability administration, our
first step in the direction of serving to Go builders study identified vulnerabilities that
could have an effect on them.
This put up gives an outline of what’s out there at this time and subsequent steps for this undertaking.
Overview
Go gives tooling to research your codebase and floor identified vulnerabilities.
This tooling is backed by the Go vulnerability database,
which is curated by the Go safety workforce.
Go’s tooling reduces noise in your outcomes by solely surfacing vulnerabilities
in capabilities that your code is definitely calling.
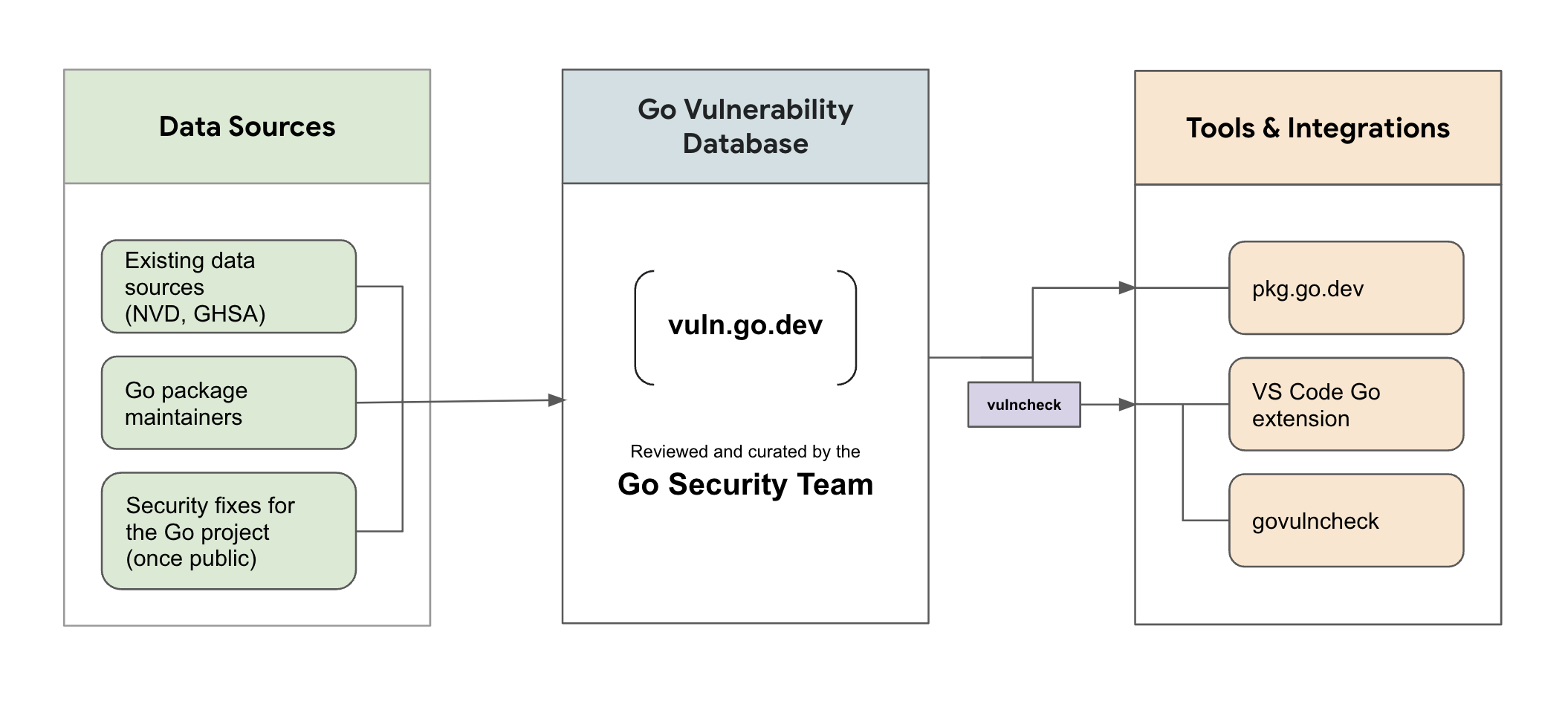
Go vulnerability database
The Go vulnerability database (https://vuln.go.dev) is a complete supply
of details about identified vulnerabilities in importable packages in public Go modules.
Vulnerability information comes from current sources (resembling CVEs and GHSAs)
and direct studies from Go bundle maintainers.
This info is then reviewed by the Go safety workforce and added to the database.
We encourage bundle maintainers to contribute
details about public vulnerabilities in their very own initiatives and replace
current details about vulnerabilities of their Go packages.
We goal to make reporting a low friction course of,
so please ship us your solutions for
any enhancements.
The Go vulnerability database may be seen in your browser at pkg.go.dev/vuln.
For extra details about the database, see go.dev/safety/vuln/database.
Vulnerability detection utilizing govulncheck
The brand new govulncheck command is a low-noise,
dependable method for Go customers to study identified vulnerabilities which will
have an effect on their initiatives.
Govulncheck analyzes your codebase and solely surfaces vulnerabilities that
truly have an effect on you,
based mostly on which capabilities in your code are transitively calling weak capabilities.
To begin utilizing govulncheck, you’ll be able to run the next out of your undertaking:
$ go set up golang.org/x/vuln/cmd/govulncheck@newest
$ govulncheck ./...
Govulncheck is a standalone instrument to permit frequent updates and speedy iteration
whereas we collect suggestions from customers.
In the long run, we plan to combine the govulncheck instrument into the principle Go distribution.
To immediately combine vulnerability checking into different instruments and processes,
the vulncheck bundle exports govulncheck’s
performance as a Go API.
Integrations
It’s at all times higher to study vulnerabilities as early as potential
within the improvement and deployment course of.
To that finish, we’ve got built-in vulnerability detection into current Go instruments and companies,
such because the Go bundle discovery website.
For instance, this web page
reveals the identified vulnerabilities in every model of golang.org/x/textual content.
Vulnerability checking performance by way of the VS Code Go extension can be coming quickly.
Subsequent Steps
We hope you’ll discover Go’s assist for vulnerability administration helpful and assist us enhance it!
Go’s assist for vulnerability administration is a brand new characteristic that’s below energetic improvement.
You need to anticipate some bugs and limitations.
We’d love so that you can contribute and assist us make enhancements within the
following methods:
We’re excited to work with you to construct a greater and safer Go ecosystem.