Microsoft API’s or API permissions for Managed Identities
However you may solely add Azure RBAC roles to a Managed Identification, proper?
That’s not true, within the weblog publish under I clarify how one can add useful resource permissions to a Managed Identification.
In my work I primarily use this for Azure Automation. By utilizing Managed Identities I not have to fret about secrets and techniques or certificates.
I’ll clarify under how we are able to add permissions to the Microsoft Graph API, however you may also use the steps under for different assets.
What do we’d like earlier than we are able to begin?
Earlier than we are able to get began we’d like the next:
- Background rationalization
- An account with world administrator permissions
- The AzureAD PowerShell module
- A customized perform
Add-ResourcePermissionsToManagedIdentitythat may be discovered on my private Github
Background rationalization
If you’re simply searching for the answer, you may skip this step.
A managed Identification is mainly an Enterprise software in Azure AD. If it’s a system assigned managed identification, it is going to additionally disappear when the Azure useful resource is deleted in Azure.
You may as well see the managed Identities below the Enterprise purposes within the Azure AD portal. See the screenshot for this.

A Useful resource is the truth is additionally an Enterprise software. You possibly can typically acknowledge it by the 0000000X AppIds.
Get-AzureADServicePrincipal -all $true | Type-Object AppId
AppId DisplayName
----- -----------
00000001-0000-0000-c000-000000000000 Azure ESTS Service
00000002-0000-0000-c000-000000000000 Home windows Azure Energetic Listing
00000002-0000-0ff1-ce00-000000000000 Workplace 365 Trade On-line
00000003-0000-0000-c000-000000000000 Microsoft GraphYou may as well see these within the Azure AD portal below Microsoft Functions.
The names aren’t all the time recognizable, however the AppId is similar.
Have a look at the screenshot under for the Microsoft Graph API.

The permissions you grant additionally obtain direct Admin consent, which is why we additionally log in with a world administrator account.
Please verify this publish from Microsoft if you wish to know extra about Managed Identities in Azure:
Managed identities for Azure assets | Microsoft Docs
An account with world administrator permissions
As you in all probability know you must give ‘admin consent’ throughout the portal earlier than a permission turns into energetic for an app registration. The identical goes for a managed identification, however that is executed ‘straight’ and can’t be executed within the Azure portal.
Neither are you able to do it with the appliance administrator position.
That’s why we’d like the worldwide administrator position.
The AzureAD PowerShell module
Including the permissions to Microsoft APIs in Azure Energetic Listing is at present solely potential by means of PowerShell.
For that motive we’d like the AzureAD PowerShell module.
You possibly can set up the module by means of PowerShell by utilizing cmdlet:
Set up-Module AzureAD -Scope CurrentUserOr obtain it straight from the PowerShell Gallery.
You possibly can log in with Join-AzureAD with the worldwide administrator account.
A customized perform Add-ResourcePermissionsToManagedIdentity
As a result of it needs to be executed through PowerShell, I’ve processed the steps in a PowerShell perform.
Copy the perform from Github and paste it into your IDE.
Because the perform is in depth, we’ll proceed within the steps under.
Let’s add useful resource permissions to a Managed Identification
The perform has 3 parameters:
- AppServicePrincipalObjectId
- Permissions
- Useful resource
ServicePrincipalObjectId
The ServicePrincipalObjectId is the ObjectId as you see it the place you enabled the Managed Identification.
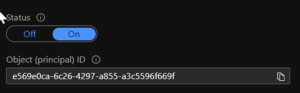
So mine is e569e0ca-6c26-4297-a855-a3c5596f669f.
Permissions
Since I additionally simply launched a brand new PowerShell module for Azure AD & Microsoft 365 reviews, I’ll take these permissions from the Microsoft Graph API for example so as to add to a Digital Machine managed identification.
- AuditLog.Learn.All
- Listing.ReadWrite.All
- Listing.Learn.All
- Stories.Learn.All
The permissions typically will be discovered on Microsoft Docs for the regarding API.
Useful resource
The Useful resource is the API title.
The perform incorporates the names with a ValidateSet, so verify fastidiously which title belongs to the API.
The default possibility is at present the Microsoft Graph API.
If you wish to know which assets have which permissions you should use the -ShowPermissionOnly change.
This will present the permissions for all assets or a selected one.
Add-ResourcePermissionsToManagedIdentity -Useful resource 'Microsoft Graph' -ShowPermissionsOnly
AllowedMemberTypes : {Software}
Description : Permits the appliance to learn the tenant-level settings of SharePoint and OneDrive, with out a signed-in person.
DisplayName : Learn SharePoint and OneDrive tenant settings
Id : 83d4163d-a2d8-4d3b-9695-4ae3ca98f888
IsEnabled : True
Worth : SharePointTenantSettings.Learn.AllWhen you don’t enter the useful resource parameter, you’ll get a listing of all assets with permissions.
Add-ResourcePermissionsToManagedIdentity -ShowPermissionsOnly
AppDisplayName : Microsoft Intune API
AppId : c161e42e-d4df-4a3d-9b42-e7a3c31f59d4
PermissionDisplayName : Handle associate compliance insurance policies with Microsoft Intune.
PermissionDescription : Permits the app to ship associate compliance insurance policies and its Azure AD Group task to Microsoft Intune with out a signed-in person.
PermissionValue : manage_partner_compliance_policy
PermissionType : Software
PermissionId : 3857e233-c379-404e-85e9-bdbf3a62b28f
PermissionIsEnabled : TrueWe follow Microsoft Graph.
The cmdlet and outcomes
We now have the next:
- AppServicePrincipalObjectId: e569e0ca-6c26-4297-a855-a3c5596f669f
- Permissions: Listing.Learn.All, AuditLog.Learn.All, Listing.ReadWrite.All, Stories.Learn.All
- Useful resource: Microsoft Graph
Now that we’ve got all the pieces collectively we are able to use the perform.
The perform makes use of the Azure AD module. First sign up with Join-AzureAD.
I take advantage of splatting to make it a bit extra seen on my weblog.
You may as well add the parameters within the regular manner.
Add-ResourcePermissionsToManagedIdentity -AppServicePrincipalObjectId 'GUID' -Permissions 'PERM' -Useful resource 'Energy BI Service'The complete cmdlet plus outcomes are under.
$ResourcePermissionsToManagedIdentity = @{
AppServicePrincipalObjectId = 'e569e0ca-6c26-4297-a855-a3c5596f669f'
Permissions = @('Listing.Learn.All','AuditLog.Learn.All','Listing.ReadWrite.All','Stories.Learn.All')
Useful resource="Microsoft Graph"
}
Add-ResourcePermissionsToManagedIdentity @ResourcePermissionsToManagedIdentity
ObjectId ResourceDisplayName
-------- -------------------
ychJil06pEGcHIYBHRFH4mzs8YyE6YxFlSPwdQxUGcs Microsoft Graph
ychJil06pEGcHIYBHRFH4lkgUimeWFxNjc7pTvPDWRc Microsoft Graph
ychJil06pEGcHIYBHRFH4s997ZgvvmlOohJ3O5Am45Y Microsoft Graph
ychJil06pEGcHIYBHRFH4kKur_yH5kdAj5gJBGRlVvg Microsoft Graph When including it for a digital machine you must restart the VM for the permissions to take impact.
Optimized.Mga now helps Managed Identities!
As you in all probability noticed within the steps above, the Optimized.Mga module now consists of an possibility for Managed Identities. And sure, your AccessToken remains to be being renewed!
I’ve examined it myself on a Digital Machine, Azure Automation, and Azure Capabilities.
Do you come throughout a Managed identification that it doesn’t work on but?
Then I’d love to listen to about it through Github or the feedback under.
You possibly can request an AccessToken as a Managed Identification through the next cmdlet:
Join-Mga -ManagedIdentityAs well as, a brand new cmdlet has been added: Present-MgaAccessToken.
With this cmdlet you may instantly see which roles your app registration has.
Join-Mga -ManagedIdentity
Present-MgaAccessToken -Roles
You've got efficiently created an AccessToken for the Microsoft.Graph.API
Listing.ReadWrite.All
Listing.Learn.All
Stories.Learn.AllOptimized.Aza now additionally helps Managed Identities!
As you in all probability noticed within the steps above, the Optimized.Mga module now consists of an possibility for Managed Identities. And sure, your AccessToken remains to be being renewed!
I’ve examined it myself on a Digital Machine, Azure Automation, and Azure Capabilities.
Do you come throughout a Managed identification that it doesn’t work on but?
Then I’d love to listen to about it through Github or the feedback under.
You possibly can request an AccessToken as a Managed Identification through the next cmdlet:
Join-Aza -ManagedIdentityAs well as, a brand new cmdlet has been added: Present-MgaAccessToken.
With this cmdlet you may instantly see which roles your app registration has.
Join-Aza -ManagedIdentity -Useful resource 'https://administration.azure.com'
You've got efficiently logged in to https://administration.azure.com