A Fast Modernisation Plan (RAMP) is important to make Purple Forests in a hybrid IT infrastructure safer. In lots of instances, corporations depend on an Enhanced Safety Admin Atmosphere (ESAE) for max safety in Energetic Listing. This strategy is a extremely safe customary for native environments with separate general constructions and Purple Forests. Nonetheless, the modernisation is required in IT constructions utilizing Entra ID.
The usage of Entra ID requires modernization
ESAE (also known as Purple Forest, Admin Forest, or Hardened Forest) is optimized for working on-premises AD environments. We suggest studying our article Deploying Purple Forest and IAM in Energetic Listing environments.
We are going to use Zero Belief and different applied sciences that reach the basic ESAE strategy to the cloud to replace extremely safe ESAE environments whereas utilizing Entra ID in parallel. The best way to this ultra-modern hybrid atmosphere runs by way of Microsoft’s Fast Modernization Plan (RAMP). On this article, we are going to present you what’s essential on this context and which new applied sciences play an essential function.
Privileged Entry Administration protects administrator accounts in Entra ID from safety threats.
RAMP with ESAE, Purple Forest and Hardened Forest
For corporations counting on the ESAE strategy and having extremely safe Purple Forests or Hardened Forests in place, RAMP helps to convey the atmosphere updated when Entra ID is utilized in parallel. RAMP integrates trendy safety applied sciences like Zero Belief and the Privileged Entry Technique into current environments to modernize them and shield towards cyber-attacks concentrating on Azure AD / Entra ID.
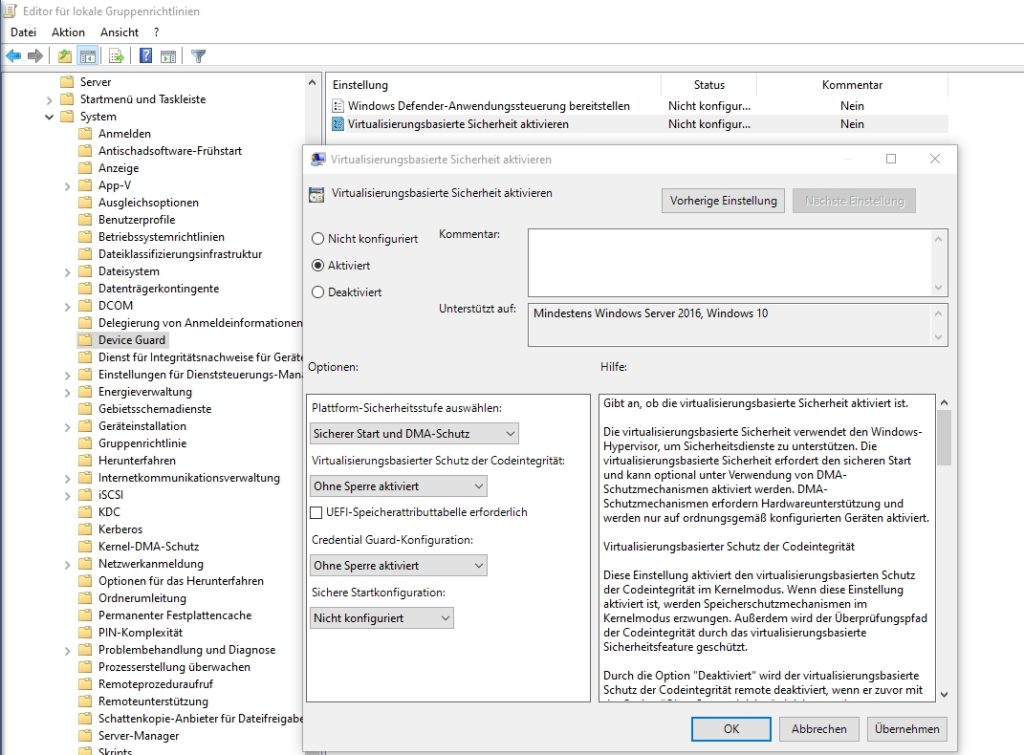
ESAE focuses on dividing servers and workstations into tiered-models for administration. Even when that is at the moment very safe, it needs to be expanded with Zero Belief and Privileged Entry Methods. In the event you use or plan to make use of Entra ID, Microsoft recommends combining Zero Belief and Privileged Entry Technique with ESAE. Microsoft helps this replace with the Fast Modernization Plan (RAMP). With this plan, corporations convey their safety atmosphere to a contemporary state, really helpful by Microsoft for integration into hybrid environments and safety towards trendy cyber-attacks.
RAMP integrates Privileged Entry Technique into Purple Forests
The main target of the Fast Modernization Plan is on implementing the Privileged Entry Technique in on-premises environments to arrange them for hybrid use and trendy cyber-attacks. The Privileged Entry Technique helps on-premises Energetic Listing and Entra ID in parallel. This new safety customary addresses safety gaps that cybercriminals can exploit to efficiently assault on-premises AD. The main target is on defending the atmosphere from more and more subtle phishing assaults. These weren’t built-in into ESAE.
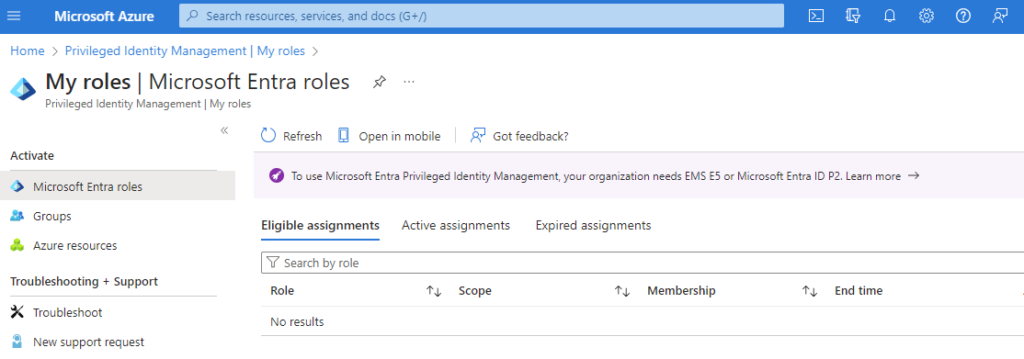
Definition and monitoring of roles for administration in AD. An Entra ID Premium P2 or EMS E5 subscription is required.
RAMP integrates the Privileged Entry Technique to guard not solely AD and Entra ID but additionally crucial enterprise functions. These functions could also be within the cloud and linked to Entra ID. Consumer accounts in Entra ID typically originate from AD and are synchronized by way of instruments like Entra ID Join.
To guard these new constructions, trendy safety applied sciences are wanted that transcend what ESAE was initially designed for. RAMP integrates plans and constructions to higher shield privileged person accounts, constructing on the ESAE strategy and additional growing it.
RAMP introduces emergency accounts: Breaking Glass Accounts
As privileged person accounts, together with admin accounts, are additional secured by RAMP, directors might inadvertently lock themselves out of the atmosphere, reminiscent of Entra ID and Microsoft 365 / Groups. To stop this, RAMP integrates new accounts referred to as Breaking Glass Accounts.
These are emergency accounts used when entry to the atmosphere with different admin accounts is not doable. Such accounts are essential not solely within the context of Entra ID but additionally when utilizing AWS, GCP, or different cloud providers. Establishing such accounts needs to be carried out in parallel with securing privileged accounts.
New safety providers: Entra ID Privileged Id Administration and Entra ID Id Safety
Securing accounts in Entra ID is finished by way of Azure providers like Privileged Id Administration and Id Safety. It’s anticipated that these providers will obtain new names with the renaming to Entra ID, however the functionalities will stay the identical. To make use of these providers, subscriptions to Entra ID Premium P2 or Enterprise Mobility + Safety E5 are required.
Moreover, the Simply-in-Time strategy needs to be utilized, the place privileged accounts solely get entry when wanted and for a restricted time. This is applicable not solely to Entra ID but additionally to on-premises AD environments with the ESAE strategy. Extensions to the safety construction might also be mandatory right here.
Microsoft Defender for Id to guard Entra ID and on-prem AD
For extra safety of identities in Entra ID and on-premises Energetic Listing environments, Microsoft recommends utilizing Microsoft Defender for Id. The service screens the use and administration of person accounts in on-premises Energetic Listing and, concurrently, in Entra ID.
ⓘ The administration of on-premises, hybrid, and Purple Forest person identities can be improved with IAM programs.
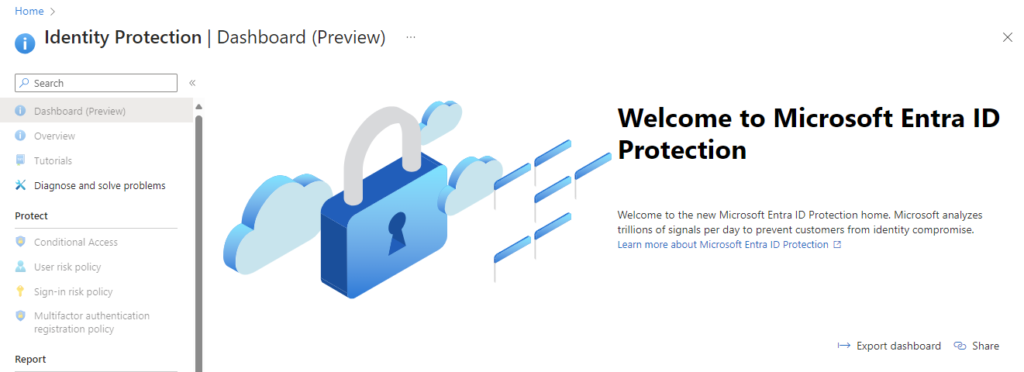
Entra ID Id Safety additionally requires a subscription to Entra ID Premium P2 or EMS E5 and is an integral a part of the Privileged Entry Technique.
When each worlds are utilized in hybrid environments, utilizing Microsoft Defender for Id is advisable. The service is a central component of the Fast Modernization Plan and the Privileged Entry Technique. It instantly detects suspicious habits of person accounts, informs directors, and automates duties to guard the atmosphere.
Modernizing on-premises Energetic Listing with RAMP
RAMP focuses not solely on securing accounts in Entra ID together with on-premises Energetic Listing but additionally on modernizing on-premises accounts. RAMP extends the present safety constructions of ESAE and brings them updated.
On-premises AD administration nonetheless happens by way of Privileged Entry Workstations (PAWs). These live on with the brand new approaches to logging in to Entra ID. Logging in to PAWs ought to solely be carried out with accounts particularly created for this function in these infrastructures.
Privileged Entry Workstations are additionally an essential pillar for extra safety as a part of Microsoft’s trendy Privileged Entry Technique.
Directors usually work with not less than two accounts. One account is used for managing Energetic Listing and is used on a PAW. The opposite account is utilized by the administrator for his or her each day work. Relying on the atmosphere, it’s doable that an admin might have a number of accounts for managing totally different environments.
It will be important on this strategy that directors don’t share accounts. RAMP clearly specifies that every administrator ought to have their very own account. If a number of directors handle an atmosphere, they want their very own account, which is used just for logging in to the PAW. This could already be the case with ESAE, however is an additional planning level because of the modernization with RAMP.
Multifactor authentication and passwordless login come into play
In Entra ID, multifactor authentication and passwordless login additionally come into play with RAMP. MFA can be utilized in native AD environments and needs to be thought of as an possibility with the intention to convey the atmosphere as much as present safety requirements.
FirstAttribute AG – Id Administration & IAM Cloud Providers
We might be completely happy to current our options to you.
Get in contact and learn how we might help you.
Did this show you how to? Share it or depart a remark:
Article created: 07.02.2024



